You use the internet for many wonderful things: connecting with family, staying informed, shopping, and managing your finances. This digital world offers incredible convenience and joy. Yet, alongside these benefits, a persistent concern exists for many, especially for adults 55 and over: online scams. Stories about people losing money or personal information can make anyone hesitant to fully embrace technology.
Whether you are catching up on news or learning how to use Amazon to shop online safely, staying vigilant is the best way to enjoy the web.
It is also helpful to learn how to recognize the grandparent scam, another common tactic that targets seniors through emotional manipulation.
You are right to be careful. Scammers are always trying new tricks. One common and particularly aggressive tactic is the tech support scam. These fraudsters pretend to be legitimate technology experts, often claiming to work for well-known companies like Microsoft or Apple, to gain your trust, access your computer, and steal your money or information. This guide will empower you with the knowledge to easily identify, understand, and avoid these deceptive schemes, giving you confidence as you navigate the digital landscape.
We believe in helping you use technology safely, without fear. Recognizing a tech support scam does not require you to be a computer expert. It simply requires knowing what to look for and what steps to take. We will walk you through the tell-tale signs, offer clear actions to protect yourself, and reassure you that if you ever encounter one of these scams, you are not alone, and it is never your fault.
Table of Contents
- What is a Tech Support Scam and Why Are They So Common?
- How Tech Support Scams Target You
- Red Flags: How to Spot a Fake Tech Support Message
- Understanding Remote Access Fraud: Giving Control to a Scammer
- What to Do If You Encounter a Tech Support Scam
- What to Do If You’ve Fallen for a Tech Support Scam
- Protecting Yourself from Future Tech Support Scams
- Reporting Tech Support Scams: Helping Others and Yourself
- Frequently Asked Questions
- Remember: It is Not Your Fault

What is a Tech Support Scam and Why Are They So Common?
A tech support scam is a type of fraud where a criminal pretends to be a legitimate technical support representative from a well-known company, such as Microsoft, Apple, or even your internet service provider. Their goal is to convince you that your computer has a serious problem, like a virus or a security threat, and then trick you into paying for unnecessary “repairs” or giving them remote access to your device. Once they have access, they can install bad software, which we call malware, steal your personal information, or lock you out of your own computer.
You can further enhance your digital security by learning how to safely use public Wi-Fi when connecting to the internet away from home.
These scams are incredibly common because they exploit a natural concern: the fear of computer problems. Many people feel a little intimidated by technology, and when they see a warning message or receive an urgent call, they understandably want to fix the problem quickly. Scammers prey on this desire for help, using urgent language and impersonating trusted brands to create a sense of panic and urgency.
You do not need to be a computer expert to protect yourself from tech support scams. Knowing the basic warning signs empowers you to stay safe online.
The consequences of falling victim to a tech support scam can be severe. The Federal Trade Commission (FTC) reported that in 2022, consumers lost over $600 million to tech support scams. The median individual loss was $1,000. These figures highlight the significant financial impact and the scale of this problem across the United States. Scammers often demand payment through unusual methods, such as gift cards or wire transfers, which are difficult to trace and recover.
How Tech Support Scams Target You
Scammers use several deceptive methods to initiate contact and hook their victims. Understanding these approaches is the first step in learning how to spot tech support scams.
If you ever encounter a malicious pop-up, it is a good idea to delete your browsing history once you close the window.
It is also wise to learn how to spot scams on social media so you don’t fall for fake tech support ads on your feed.
Beyond phone calls and emails, criminals are increasingly finding ways to avoid common scams targeting seniors on social media to find new victims.
1. Unexpected Phone Calls:
You receive an unsolicited phone call from someone claiming to be from “Microsoft Support,” “Apple Tech Support,” or even “Windows Security Department.” They often have foreign accents and speak very quickly, using technical jargon to confuse you. They might say they detected a virus on your computer or that your security has been compromised. Remember, legitimate tech companies like Microsoft and Apple do not make unsolicited calls to tell you about problems with your computer unless you have specifically requested support from them.
Example: Your phone rings, and a person says, “Hello, this is John from Microsoft technical support. We’ve detected critical security issues with your computer’s operating system. If we don’t fix it immediately, you risk losing all your data.” They press you to act right away, before you have a chance to think.
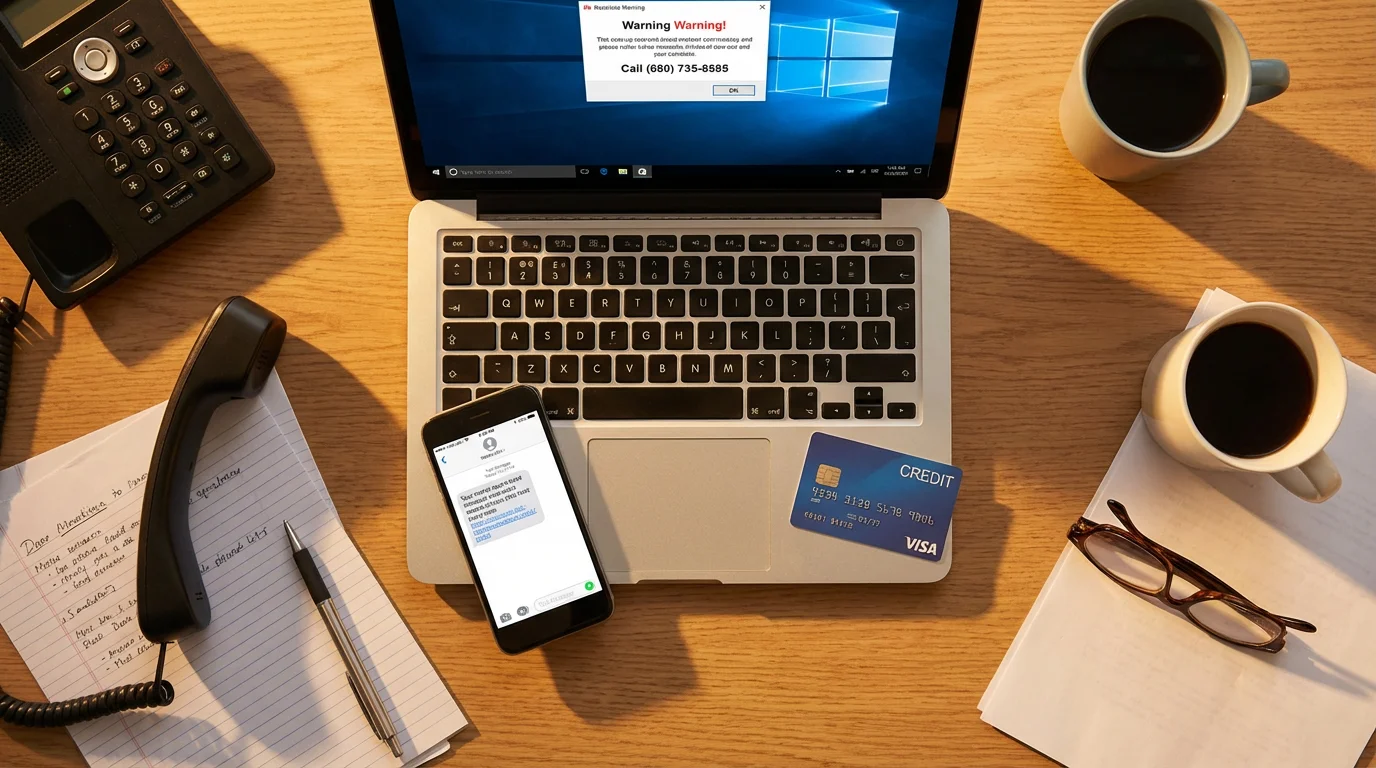
2. Alarming Pop-Up Messages:
While browsing the internet, a sudden, full-screen pop-up message appears on your computer. This pop-up often looks very official, sometimes even mimicking the Windows or Apple operating system interface. It usually contains frightening warnings like “Your computer is infected with multiple viruses!” or “Critical system error detected! Call this number immediately for assistance.” The pop-up might even include loud, repetitive alarm sounds to heighten the sense of urgency. These messages often freeze your web browser, making it difficult to close them.
Example: You are reading an article online, and suddenly your screen goes dark, showing a bright red box with a skull icon. It flashes, “WARNING! YOUR SYSTEM IS COMPROMISED! CALL 1-800-XXX-XXXX FOR IMMEDIATE REPAIR. DO NOT SHUT DOWN YOUR COMPUTER.” This is a tactic to panic you into calling their fake number.
3. Fake Emails and Text Messages (Phishing):
You might receive emails or text messages that appear to be from a well-known tech company. These messages often contain urgent warnings about your account security or computer health and instruct you to click a link or call a phone number for assistance. This is a type of phishing scam, where criminals send fake communications to trick you into revealing personal information or downloading harmful software. The links in these emails often lead to malicious websites or download bad software, known as malware, onto your device.
Example: You get an email with the subject line “Urgent Security Alert for Your Apple ID.” The email body states that unusual activity has been detected on your account and asks you to click a link to “verify your identity” or call a number. The email might look convincing, using company logos, but the sender’s email address is often slightly off, or the grammar might be poor.
In all these scenarios, the scammer’s goal is the same: to create panic, establish trust by impersonating a legitimate company, and then either get you to pay for bogus services or grant them access to your computer.

Red Flags: How to Spot a Fake Tech Support Message
Knowing the common methods scammers use helps you recognize their initial attempts. Now, let’s look at specific warning signs that tell you the person or message you are dealing with is likely a scam. These red flags are your personal alarm system.
If you use your phone for finances, make sure you understand how to use mobile banking apps safely to avoid unauthorized transfers.
- Unsolicited Contact: Did they contact you first? Legitimate tech support companies generally do not call you out of the blue about a problem with your computer. They also do not send pop-ups that lock your browser and demand you call them. If you did not initiate the contact, be immediately suspicious.
- Urgency and Pressure: Scammers always try to rush you. They insist you must act “immediately” or “your computer will be destroyed,” “your bank account will be emptied,” or “all your data will be lost.” They do not give you time to think, consult with a family member, or verify their claims. Real tech support understands you need time to assess a situation.
- Demands for Remote Access: The scammer will almost always ask you to download software that gives them remote access to your computer. This means they can see everything on your screen and control your mouse and keyboard. While legitimate tech support sometimes uses remote access, they only do so after you have initiated contact and verified their identity, and certainly not during an unsolicited call or after a frightening pop-up.
- Requests for Unusual Payment Methods: Scammers frequently demand payment via gift cards, wire transfers, cryptocurrency, or peer-to-peer payment apps like Zelle or Venmo. They prefer these methods because they are nearly impossible to trace and recover once sent. Legitimate companies typically accept credit cards or established online payment systems and provide invoices for services.
- Requests for Personal Information: They might ask for sensitive details like your bank account numbers, Social Security number, or full credit card information over the phone or through unverified websites. A legitimate tech support company rarely needs this level of personal financial detail just to fix a computer issue.
- Exaggerated Problems or Jargon: Scammers often invent complex-sounding “problems” on your computer, using intimidating technical terms you might not understand. They might show you a screen full of harmless system logs and claim these are “critical errors” or “malicious infections.” They intend to overwhelm and confuse you.
- Threats or Intimidation: Some scammers might threaten to block your computer, delete your files, or report you to authorities if you do not comply. This is a common tactic to instill fear and force your hand.
- Fake-Looking Pop-Ups or Websites: If a pop-up appears with bad grammar, misspelled words, or pixelated logos, it is a strong sign of a scam. Similarly, if an email link takes you to a website that does not look quite right, or has a strange web address, it is likely fraudulent.
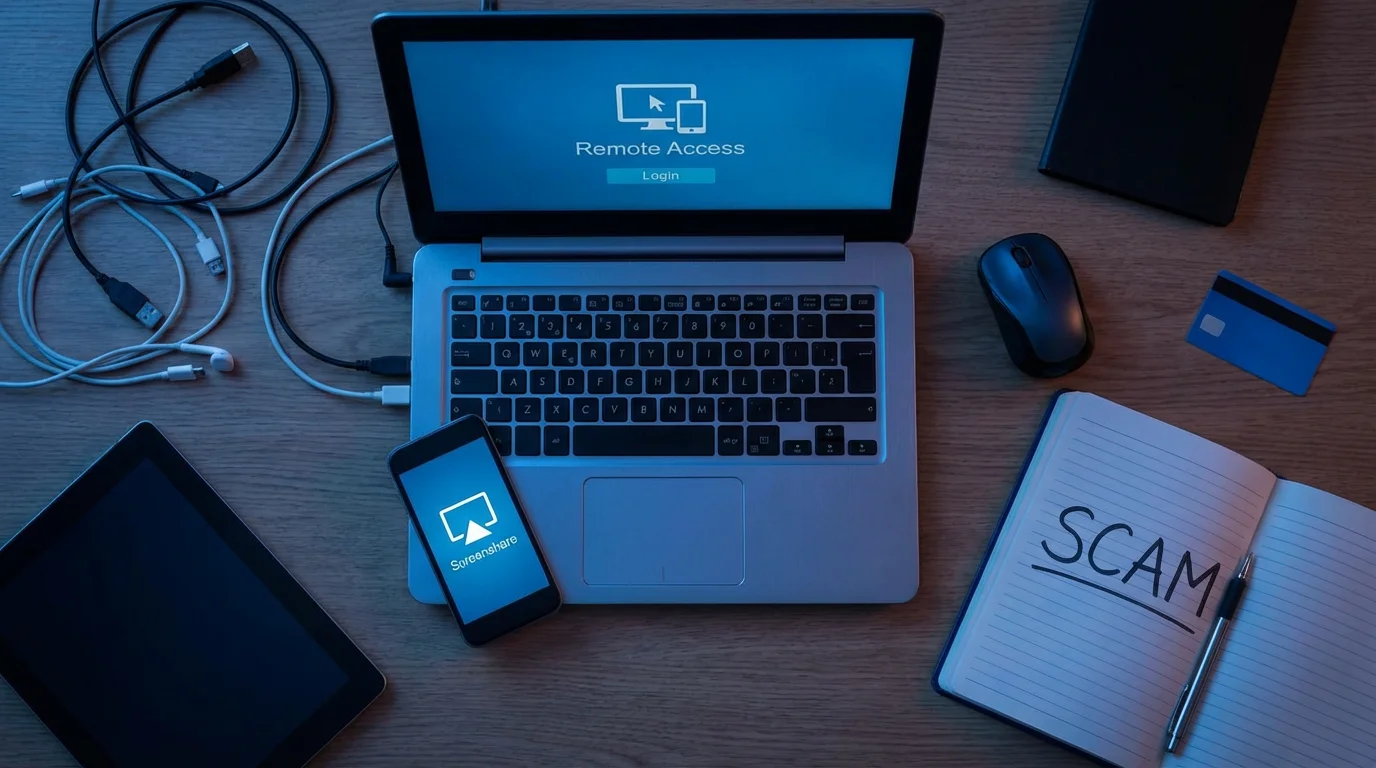
Understanding Remote Access Fraud: Giving Control to a Scammer
One of the most dangerous aspects of a tech support scam is when you grant the scammer remote access to your computer. Remote access software allows another person to view and control your computer from a different location, often thousands of miles away. Legitimate companies use this tool responsibly, for example, when a trusted IT professional helps you fix a complex issue after you have contacted them for support.
Using a password manager to stay safe online can help protect your accounts if someone ever gains access to your device.
Scammers, however, abuse remote access. They trick you into downloading and installing programs like TeamViewer, AnyDesk, or other similar tools. Once installed and activated, they gain full control over your machine. Here is what they can do:
- Install Malware: They can download bad software, known as malware, onto your computer. This malware can steal your passwords, banking information, or even encrypt your files and demand a ransom to unlock them.
- Steal Personal Information: With remote access, they can navigate through your files, documents, and even your web browser history to find sensitive personal information, account logins, and financial details.
- Change Your Settings: They can alter your computer’s security settings, making it easier for them to access your system again in the future or making it harder for you to regain control.
- Plant Fake Evidence: They might open legitimate system files and pretend these show “errors” or “viruses” to further convince you that your computer is severely compromised and that you need their help. They might even open your bank website and pretend to “secure” your account, while secretly transferring money out.
- Lock You Out: In some cases, after they have finished their scam, they might change your computer’s password or install software that locks you out of your own device, demanding more money to restore access.
You must understand that giving a scammer remote access is like handing them the keys to your home. They can walk in, look through your possessions, and take what they want without you knowing until it is too late. Always be extremely cautious about any request to install remote access software on your computer, especially if the request comes from someone you did not initiate contact with.

What to Do If You Encounter a Tech Support Scam
Knowing what to do when a tech support scam attempts to reach you is crucial. Your quick and decisive action can protect your information and your money.
If You Receive an Unsolicited Call:
- Hang Up Immediately: Do not engage in conversation. Do not press any numbers. Simply end the call.
- Do Not Call Back: The number might be spoofed, meaning it looks legitimate but is not. Calling back only confirms your number is active and could lead to more scam calls.
- Block the Number: If possible, block the number on your phone. Most smartphones allow you to block unwanted callers directly from your call history.
If a Pop-Up Appears on Your Screen:
- Do Not Call the Number: Never call any phone number listed on a suspicious pop-up.
- Close Your Browser Safely:
- On Windows: Press
Alt + F4to close the active window. If that does not work, try pressingCtrl + Shift + Escto open the Task Manager, select your browser from the “Apps” list, and click “End task.” - On Mac: Press
Command + Option + Escto open the “Force Quit Applications” window, select your browser, and click “Force Quit.”
- On Windows: Press
- Restart Your Computer: If the pop-up persists or freezes your system, restart your computer. This often clears the pop-up.
- Run a Scan: After restarting, run a full scan with your legitimate antivirus software to check for any unwanted software that might have been downloaded.
If You Receive a Suspicious Email or Text Message:
- Do Not Click Links or Open Attachments: Malicious links or attachments can install malware on your device or lead you to fake websites designed to steal your information.
- Do Not Reply: Replying confirms your email address or phone number is active.
- Delete the Message: Remove the suspicious email or text message from your inbox.
- Report Phishing: You can often report phishing emails to your email provider or forward them to the Anti-Phishing Working Group at reportphishing@apwg.org.
Your best defense against a tech support scam is prevention. Do not engage, do not click, and do not call back.
What to Do If You’ve Fallen for a Tech Support Scam
Scammers are clever, and their tactics can be very convincing. Falling for a trick does not make you foolish; it simply means you encountered a sophisticated fraudster. If you realize you have been scammed, take immediate action. The sooner you act, the better your chances of limiting the damage.
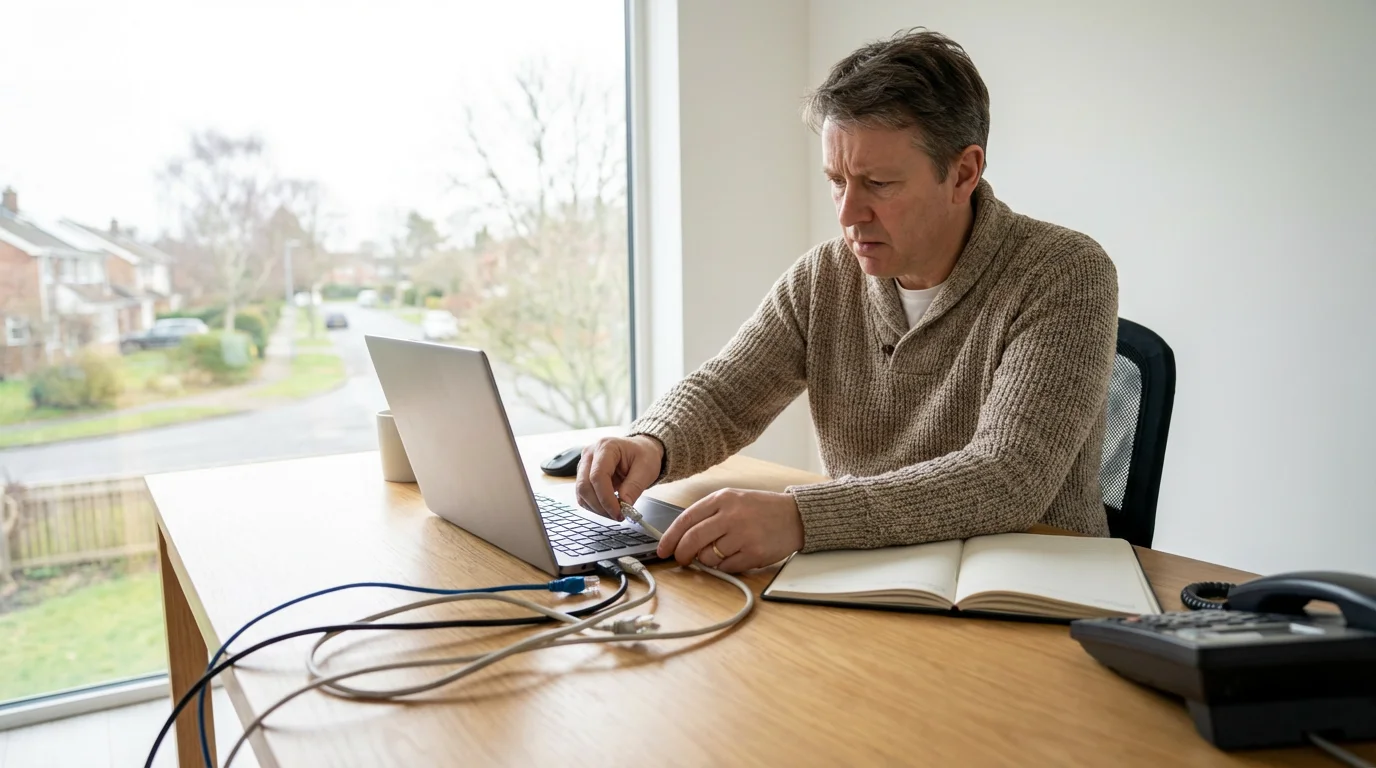
1. Disconnect Your Computer from the Internet:
If you gave a scammer remote access to your computer, immediately disconnect it from the internet. Unplug the Ethernet cable or turn off your Wi-Fi. This cuts off their access and prevents them from doing further damage or stealing more information.
2. Contact Your Bank or Credit Card Company:
If you paid the scammer with a credit card, debit card, or bank transfer, contact your financial institution immediately. Explain that you have been a victim of fraud. They can cancel transactions, freeze your accounts, and help you dispute charges. Time is critical here, as some payment methods offer more protection than others, especially if you act quickly.
3. Change All Your Passwords:
Assume the scammer now has access to your passwords, especially for online banking, email, and any accounts you accessed while they had remote control. Change these passwords immediately from a different, secure device if possible, such as a family member’s computer or a trusted smartphone. Focus on your most critical accounts first. Remember to create strong, unique passwords for each account. Consider using a password manager to help you with this.
4. Scan Your Computer for Malware:
Even if you disconnected immediately, the scammer might have installed bad software, or malware, on your computer. Use a reputable antivirus or anti-malware program to perform a full scan. If your current software is not up to date, consider using a trusted, free scanner from a well-known company like Malwarebytes or Avast (download from their official websites only).
5. Undo Any Changes They Made (If Possible):
If you know the scammer changed specific settings on your computer, revert them if you feel comfortable doing so. For instance, if they disabled your firewall, re-enable it. If you are unsure, consult a trusted, local computer technician who can safely inspect and clean your computer.
6. Report the Scam:
Reporting is a vital step. It helps law enforcement track these criminals and prevents others from falling victim. You should report the incident to:
- The Federal Trade Commission (FTC) at ReportFraud.ftc.gov or call 1-877-382-4357.
- The FBI’s Internet Crime Complaint Center (IC3). This is especially important if you lost money.
- Your local police department, particularly if you suffered financial losses.
7. Be Wary of Recovery Scams:
Unfortunately, after you fall for one scam, you might become a target for “recovery scams.” These are fraudsters who contact you, claiming they can help you get your money back from the original scammer, usually for an upfront fee. Never pay someone to recover money you lost in a scam. Real law enforcement or consumer protection agencies will never ask for payment to help you.
Remember, experiencing a scam can be distressing. Do not hesitate to reach out to a trusted family member or friend for support as you work through these steps.

Protecting Yourself from Future Tech Support Scams
While reacting quickly to a scam is important, proactive measures offer the strongest defense. By building good digital habits, you can significantly reduce your risk of encountering or falling for future tech support scams.
1. Educate Yourself Continuously:
Stay informed about common scams and new tactics. Resources like the AARP Fraud Watch Network and the FTC’s Consumer Information website regularly publish updates on current threats. The more you know, the better equipped you are to recognize a scam.
2. Use Strong, Unique Passwords and a Password Manager:
Create complex passwords for all your online accounts. A strong password uses a mix of uppercase and lowercase letters, numbers, and symbols, and is at least 12 characters long. Never reuse passwords across different accounts. A password manager is a secure application that remembers all your passwords for you, generating complex ones and filling them in automatically, so you only need to remember one master password. This drastically improves your security.
3. Enable Two-Factor Authentication (2FA) Everywhere Possible:
Two-factor authentication (also called multi-factor authentication) adds an extra layer of security to your accounts. After entering your password, you also need to provide a second piece of information, such as a code sent to your phone or generated by an authenticator app. This means that even if a scammer steals your password, they cannot access your account without that second piece of information.
4. Keep Your Software Updated:
Regularly update your operating system (Windows, macOS, iOS, Android) and all your applications, especially your web browser and antivirus software. These updates often include critical security patches that protect against known vulnerabilities exploited by scammers and malware. Set your devices to update automatically if you feel comfortable doing so.
5. Use Reputable Antivirus and Firewall Software:
Install and maintain a high-quality antivirus program from a trusted brand. Ensure your computer’s firewall is enabled. These tools act as a barrier against malware and can detect suspicious activity on your computer. Make sure your antivirus definitions are updated regularly.
6. Be Skeptical of Unsolicited Contact:
If someone calls, emails, or texts you unexpectedly about a computer problem, assume it is a scam until proven otherwise. Hang up the phone. Delete the email. Block the sender. Legitimate companies do not operate this way.
7. Verify Contact Information Independently:
If you genuinely believe you have a computer problem, or you want to verify if a message is legitimate, do not use the phone number or link provided by the suspicious contact. Instead, independently look up the official contact information for the company (e.g., Microsoft, Apple, your bank) from their official website or a trusted source. Call the number you found, not the one given to you.
8. Back Up Your Data:
Regularly back up your important files and documents to an external hard drive or a reputable cloud storage service. This protects your data even if your computer is compromised or locked by a scammer.
9. Consult Trusted Resources:
If you are ever unsure about a technology issue, consult a trusted family member, a local reputable computer technician, or official resources like the Cybersecurity & Infrastructure Security Agency (CISA) or National Cyber Security Alliance (NCSA). Never rely on the advice of someone who contacted you unexpectedly.

Reporting Tech Support Scams: Helping Others and Yourself
Reporting a tech support scam, whether you fell for it or just encountered an attempt, is a powerful action. It contributes to a larger effort to track down criminals, disrupt their operations, and protect other potential victims. Your report, combined with thousands of others, creates a clearer picture for law enforcement and consumer protection agencies.
Here are the key places to report tech support scams:
1. Federal Trade Commission (FTC):
The FTC is the primary government agency in the United States that collects reports about fraud, identity theft, and deceptive business practices. They use these reports to investigate, bring cases against scammers, and share information with other law enforcement agencies.
- Online: Visit ReportFraud.ftc.gov. This is the quickest and most efficient way to submit a detailed report.
- By Phone: Call 1-877-FTC-HELP (1-877-382-4357).
Even if you did not lose money, report the scam attempt. The FTC uses this information to identify trends and warn the public.
2. FBI Internet Crime Complaint Center (IC3):
If you lost money or sensitive personal information due to a tech support scam, or if the scam involved activity across state lines or international borders, you should also file a report with the FBI’s IC3. They collect intelligence on internet crimes and refer complaints to appropriate law enforcement agencies.
- Online: Visit www.ic3.gov. Provide as much detail as possible about the scam, including phone numbers, email addresses, websites, and how you paid.
3. Your Local Police Department:
If you lost money, especially a significant amount, or if you believe the scam involved identity theft, file a report with your local police department. While they might not actively investigate every online scam, having a police report can be essential for disputing fraudulent charges with your bank or credit card company. They can provide you with a case number which is often required for financial recovery efforts.
4. Better Business Bureau (BBB) Scam Tracker:
The Better Business Bureau (BBB) Scam Tracker allows you to report scams and read about scams reported by others in your area. This helps raise public awareness and provides valuable insights into current scam trends. While the BBB does not have law enforcement powers, their tracker serves as a public warning system.
5. Your Bank or Credit Card Company:
As mentioned, if you made any payments to a scammer, immediately contact your financial institution. They need to know about the fraudulent activity to protect your accounts and potentially recover funds.
Your reports are valuable. They help authorities understand the scope of these scams, gather evidence, and ultimately work towards bringing these criminals to justice. By reporting, you play an active role in making the internet a safer place for everyone.
Frequently Asked Questions
Q: What if I already clicked a pop-up or shared information?
A: Do not panic. If you clicked a suspicious link or gave information, immediately disconnect your computer from the internet. Then, contact your bank or credit card company if you shared financial details. Change all your important passwords, starting with banking and email, using a different, secure device. Finally, run a full scan with reputable antivirus software on your computer. Report the incident to the FTC at ReportFraud.ftc.gov and the FBI IC3 at www.ic3.gov if you lost money or sensitive data.
Q: How do I know if a call is really from my bank or a legitimate company?
A: Legitimate companies and banks will rarely, if ever, call you out of the blue asking for sensitive information or demanding immediate action on your computer. If you receive an unexpected call, hang up. If you are concerned that there might be a real issue, independently look up the company’s official phone number from their website or a trusted statement, and call them back yourself. Do not use any number the caller provided.
Q: Can scammers really get into my computer from a pop-up?
A: A pop-up itself does not automatically give scammers access to your computer. However, if you call the number on the pop-up and follow their instructions to download software or give them remote access, then they absolutely can get into your computer. The pop-up is a trick to get you to contact them, not a direct gateway.
Q: Should I ever give someone remote access to my computer?
A: Only give remote access to a trusted, legitimate technical support professional whom you have contacted directly and whose identity you have verified. Never give remote access to anyone who calls you unexpectedly, sends you an alarming pop-up, or asks for unusual payment methods. Always be extremely cautious, as remote access gives someone full control over your device.
Q: What is the best way to keep my computer safe from these scams?
A: The best way to protect yourself involves several layers of defense: remain skeptical of unexpected contact, keep your operating system and antivirus software updated, use strong unique passwords for all accounts, and enable two-factor authentication wherever possible. Remember that legitimate tech support will not initiate contact with you about a problem or ask for payment in gift cards. If in doubt, do not engage and seek advice from a trusted source.
Remember: It is Not Your Fault
Experiencing a tech support scam, or even just being targeted by one, can feel unsettling. It is important to remember that these scammers are professionals at deception. They invest significant time and effort into creating convincing scenarios, exploiting human nature, and using sophisticated psychological tricks to manipulate people. Their tactics are designed to make you feel panicked, rushed, and vulnerable. If you have ever felt confused or even fallen for one of their ploys, know that you are in good company. Millions of people, across all ages and levels of tech savviness, have been targeted.
Your goal is not to become a cybersecurity expert overnight, but to gain confidence in recognizing common threats. By learning the red flags and understanding what actions to take, you empower yourself to navigate the digital world with greater security. You are taking positive steps to protect your personal information and your finances.
Scammers are cunning and resourceful. If you encountered a scam, it means you crossed paths with a skilled manipulator, not that you made a mistake. Your vigilance makes a difference.
We encourage you to share this information with your friends and family. A strong, informed community is our best defense against these frauds. Keep learning, stay vigilant, and remember that you have the power to stay safe online.
Disclaimer: This article provides general information about online safety and is not a substitute for professional advice. If you believe you’ve been a victim of fraud, contact your bank immediately and report the incident to the FTC at ReportFraud.ftc.gov or call 1-877-382-4357. If you’ve lost money, also file a report with your local police.











Leave a Reply